By 2026, the traditional security perimeter is not just dissolving; it’s a liability for UAE enterprises that still rely on legacy silos. With the UAE Federal Decree Law No. 45 of 2021 (PDPL) setting a high bar for data sovereignty, a generic cloud data loss prevention strategy is no longer enough to protect your reputation in a competitive global market. You’ve likely dealt with the exhaustion of managing 500 false-positive alerts a day or the anxiety of “shadow IT” applications appearing across your multi-cloud environment without oversight. We agree that security shouldn’t be a bottleneck that prevents your team from moving at the speed of innovation.
This architectural guide helps you master the transition to a resilient, cloud-native DLP framework that balances rigorous protection with business agility. You’ll gain a structured roadmap to eliminate visibility gaps and ensure your security tools work in harmony with your human workflows. We’ll examine how bespoke architectural choices can reduce your regulatory risk while future-proofing your digital infrastructure for the next decade of growth in the Emirates.
Key Takeaways
- Understand why legacy, network-centric perimeters fail in distributed environments and how to transition toward a resilient, cloud-native security framework.
- Discover how to build a robust cloud data loss prevention strategy using AI-driven continuous discovery and dynamic classification across SaaS, PaaS, and IaaS.
- Solve the “Friction Paradox” by integrating Zero Trust architecture to verify every data access request while maintaining high operational velocity.
- Learn to execute a technical security assessment that aligns your data protection protocols with UAE national laws and GRC frameworks.
- Explore how a bespoke architectural approach integrates Managed Detection and Response (MDR) to future-proof your enterprise against evolving digital threats.
The Evolution of Data Protection: Why Traditional DLP Fails in the Cloud
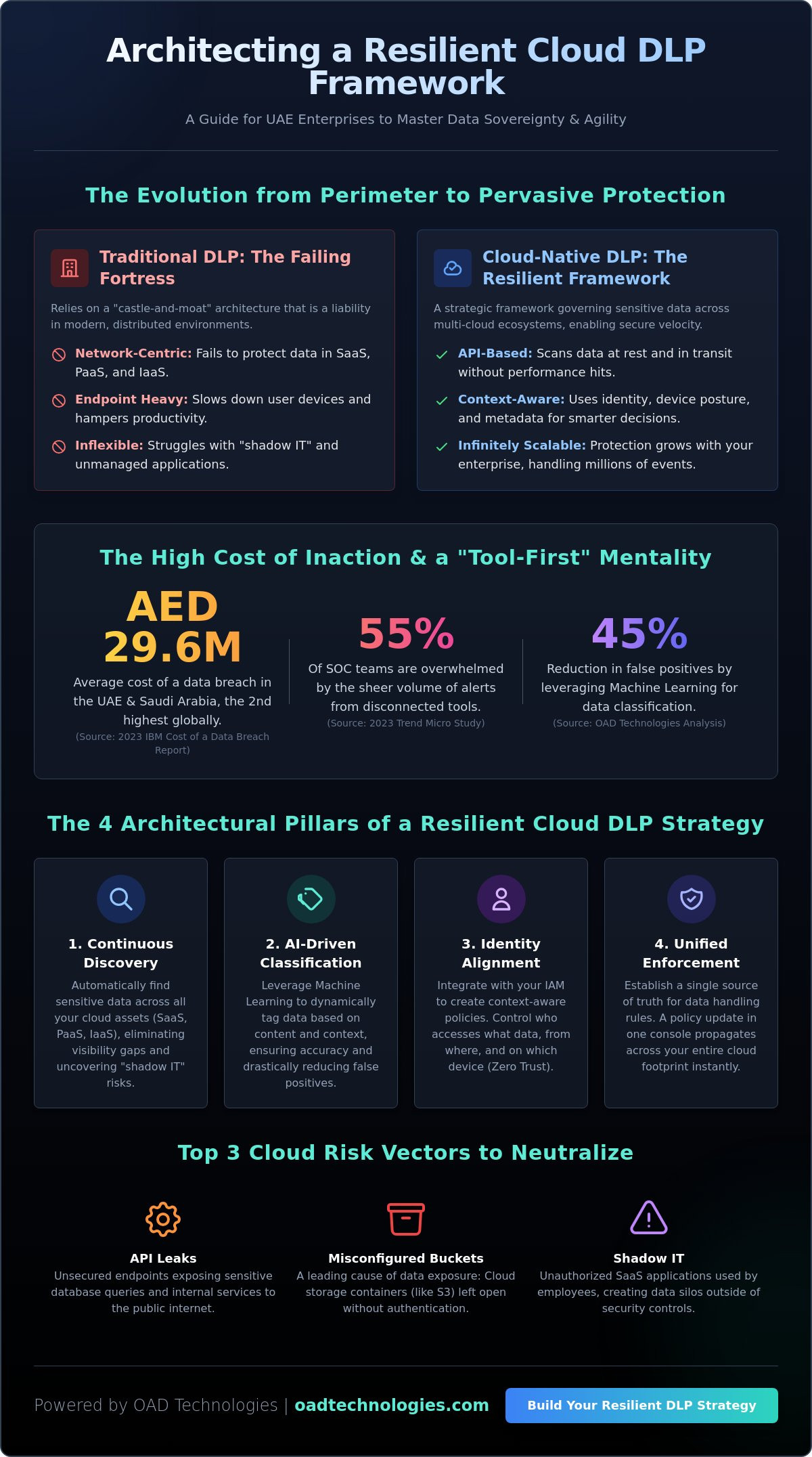
A robust cloud data loss prevention strategy is no longer a luxury for UAE enterprises; it’s a foundational requirement for digital resilience. We define Cloud DLP not as a single software purchase, but as a strategic framework designed to govern sensitive information across multi-cloud environments. Traditional security models relied on a castle-and-moat architecture, but this perimeter has dissolved. According to the 2023 IBM Cost of a Data Breach Report, the average cost of a breach in the UAE and Saudi Arabia reached AED 29.6 million, the second-highest globally. This figure underscores the failure of legacy, network-centric tools to protect distributed assets.
The “Perimeter Paradox” highlights a critical flaw: legacy systems were built for fixed endpoints and local servers. In modern architectures, data moves through APIs, resides in misconfigured S3 buckets, and is often handled by shadow IT applications that bypass central IT oversight. We’ve shifted our focus from simply blocking data movement to enabling secure data velocity. Organizations must allow data to flow to drive innovation while maintaining granular control. Implementing a comprehensive cloud data loss prevention strategy allows UAE businesses to meet the stringent requirements of Federal Decree-Law No. 45 of 2021 while maintaining operational agility.
Cloud DLP vs. Traditional DLP: Key Technical Differentiators
Traditional DLP relies on content-aware inspection at the endpoint, which often slows down user devices. Cloud-native solutions use API-based integration to scan data at rest and in transit within SaaS and IaaS platforms. This approach leverages metadata and environmental context, such as user identity or device posture, to make informed decisions. Scalability is the primary differentiator. A cloud-native engine handles millions of events per second without the hardware constraints of legacy appliances, ensuring protection grows with the enterprise.
The High Cost of a “Tool-First” Mentality
Purchasing disconnected security tools creates fragmented visibility. When systems don’t communicate, security operations center (SOC) teams face extreme alert fatigue. A 2023 study by Trend Micro found that 55% of SOC teams are overwhelmed by the volume of alerts, leading to critical gaps in threat detection. Relying on a tool-first approach increases the risk of a breach because it ignores the human and procedural elements of security. Cloud DLP is a bespoke strategy that integrates people, process, and technology to ensure long-term data sovereignty.
- API Leaks: Unsecured endpoints that expose sensitive database queries to the public internet.
- Misconfigured Buckets: Storage containers left open without authentication, a leading cause of data exposure in 2024.
- Shadow IT: The use of unauthorized SaaS applications that store corporate data outside of sanctioned security controls.
The Architectural Pillars of a Resilient Cloud DLP Strategy
Building a resilient cloud data loss prevention strategy requires moving beyond legacy “moat-and-castle” mentalities. In the distributed environments typical of Dubai’s financial hubs or Abu Dhabi’s energy sector, data doesn’t stay in one place. It flows between SaaS applications, PaaS databases, and IaaS buckets. A modern architecture relies on four non-negotiable pillars: continuous discovery, AI-driven classification, identity alignment, and unified enforcement. These pillars ensure that protection follows the data, regardless of where it resides or how it’s accessed.
OAD Technologies views these pillars not as isolated tools, but as a bespoke ecosystem. For instance, aligning DLP policies with robust identity and access management (IAM) creates a context-aware security layer. When you know exactly who is accessing what, and from where, you can apply granular restrictions that prevent unauthorized exfiltration without hindering legitimate workflows. This unified approach provides a single source of truth for data handling rules, ensuring that a policy update in your central console propagates across your entire cloud footprint instantly.
Data Discovery and Classification at Scale
Traditional manual tagging can’t keep up with the 2.5 quintillion bytes of data generated daily. Effective strategies now utilize machine learning to automate the discovery of sensitive information across unstructured cloud environments. By leveraging ML, organizations can reduce false positives by up to 45%, allowing security teams to focus on genuine threats. Persistent labeling and tagging are vital here; they ensure that once a document is classified under the UAE Federal Decree-Law No. 45 of 2021, that classification remains embedded in its metadata. This metadata guides automated controls, ensuring that a file marked as “Highly Confidential” can’t be shared via a public link, even if a user tries to move it to a different cloud tier.
Integrating DLP with Cloud Security Posture Management (CSPM)
Data doesn’t always exit through a malicious hack; often, it simply leaks through an open door. Understanding how cloud security posture management (CSPM) identifies the “leaky pipes” is critical for preventing accidental exposure. CSPM tools scan for infrastructure misconfigurations, such as unencrypted S3 buckets or overly permissive API keys, which are responsible for nearly 80% of cloud data breaches. By integrating DLP with CSPM, you close the gap between infrastructure health and data security. This synergy allows your team to prioritize remediation efforts on high-risk assets that contain the most sensitive intellectual property. If you’re looking to refine your current framework, our team can help you design a bespoke security roadmap that aligns with your specific operational needs.
Solving the Friction Paradox: Zero Trust and AI Integration
Security leaders in the UAE often face a persistent dilemma: the more rigorous the security, the slower the business moves. Historically, data protection meant rigid barriers that stifled the agility required in competitive markets like Dubai and Abu Dhabi. By 2026, a sophisticated cloud data loss prevention strategy must resolve this friction paradox. We no longer view security as a binary choice between “open” and “blocked.” Instead, we utilize intelligent, adaptive frameworks that allow data to flow securely while maintaining compliance with the UAE Data Protection Law (Federal Decree-Law No. 45 of 2021).
Modern DLP architecture shifts the focus from the perimeter to the data itself. It’s about creating a bespoke environment where security protocols understand the nuance of business operations. This evolution ensures that your high-performing teams don’t feel the weight of the security engine; they only feel the stability it provides.
Adopting a Zero Trust Model for Data Access
The Zero Trust model operates on a simple, uncompromising premise: never trust, always verify. In a cloud-first environment, identity is the new perimeter. We apply the principle of least privilege to ensure users only interact with the specific data sets required for their roles. This approach is vital for UAE enterprises that rely on a global workforce and third-party vendors.
- Contextual Awareness: Our systems evaluate user behavior, device integrity, and geographic location in real-time. A login from a registered device in Dubai Media City is treated differently than an access attempt from an unknown IP during off-peak hours.
- Blast Radius Reduction: By segmenting data access, we ensure that a single compromised credential doesn’t lead to a total system breach. This containment strategy is essential for maintaining operational continuity.
- Dynamic Verification: Authentication isn’t a one-time event at login. It’s a continuous process that monitors the session’s risk profile as the user moves between cloud applications.
Leveraging AI and Automation for Strategic Growth
Automation is the catalyst that transforms a cloud data loss prevention strategy from a reactive cost center into a driver of operational efficiency. AI doesn’t just replace manual effort; it enhances human intelligence by filtering out the noise. Statistics show that AI-driven security tools can reduce the time to identify and contain a breach by up to 100 days, significantly protecting the brand’s ROI.
We implement AI to detect anomalous data movement patterns that a human analyst might miss. If an employee suddenly downloads 50GB of proprietary financial data—an action that deviates from their 180-day baseline—the system intervenes instantly. This isn’t just about blocking; it’s about “Human-in-the-Loop” education. When a low-risk policy violation occurs, the system sends a real-time notification to the user. This immediate feedback loop trains employees on best practices, turning every staff member into a proactive guardian of company assets. This collaborative approach ensures that technology empowers your people rather than restricting their potential.
A Roadmap to Implementing a Bespoke Cloud DLP Strategy
A resilient cloud data loss prevention strategy isn’t a product you purchase off the shelf; it’s a bespoke architecture built on five foundational pillars. Execution begins with a Technical Security Assessment to map every shadow IT application and exposed API. This initial audit often reveals that up to 35% of sensitive data resides in unauthorized cloud silos. Once visibility is established, we align the technical roadmap with your Governance, Risk, and Compliance (GRC) framework. This step bridges the gap between technical execution and legal liability, ensuring every byte of data follows a defined path.
The implementation moves through three additional critical phases:
- Policy Definition: We create granular data handling rules based on business-critical use cases, avoiding the “block-all” approach that stifles productivity.
- Architectural Integration: We deploy an integrated stack consisting of Cloud Access Security Brokers (CASB), DLP engines, and Identity and Access Management (IAM) tools.
- Continuous Refinement: We establish a cycle of continuous monitoring to refine policies as your cloud footprint expands.
Regulatory Alignment and the UAE PDPL
The UAE Personal Data Protection Law (PDPL), Federal Decree Law No. 45 of 2021, imposes strict requirements on data residency and cross-border transfers. A bespoke cloud data loss prevention strategy ensures that “Sensitive Personal Data” remains within sovereign borders or moves only through approved, encrypted channels. By mapping DLP controls directly to PDPL articles, enterprises can automate up to 65% of the documentation required for external audits. This technical rigor transforms compliance from a reactive burden into a proactive shield for enterprise resilience, ensuring you meet national sovereignty standards without sacrificing global connectivity.
Phased Implementation: Avoiding Operational Disruption
Abruptly blocking traffic causes friction and leads users to find insecure workarounds. We recommend starting in “Monitoring Mode” for the first 45 days of any rollout. This period allows us to observe data flows and identify false positives without interrupting active workflows. By selecting high-impact, low-friction use cases for initial enforcement, such as preventing the upload of unencrypted PII to public storage, organizations see immediate ROI. We’ve observed that this structured, phased rollout can reduce incident response times by 32% within the first quarter of deployment. This approach measures success through prevented leaks rather than just blocked packets.
Future-Proofing Resilience: The OAD Technologies Approach
OAD Technologies views security as a high-stakes architectural craft rather than a simple procurement exercise. We don’t treat a cloud data loss prevention strategy as a commodity or a “set-and-forget” software license. By 2026, the UAE’s digital economy will demand far more than generic templates. Local enterprises must navigate the complexities of Federal Decree-Law No. 45 of 2021 while managing hyper-scaled cloud environments. We build bespoke systems that recognize your data’s specific value, ensuring that rigorous protection never throttles operational performance.
True resilience emerges when you bridge the gap between visibility and decisive action. Our methodology integrates Managed Detection and Response (MDR) directly into the data protection fabric. This synergy allows organizations to identify up to 94% of unauthorized egress attempts before they escalate into full-scale breaches. We move your defense posture from reactive alerts to proactive containment, creating a unified shield that protects sensitive intellectual property across the Dubai International Financial Centre (DIFC) and beyond.
A strategic partnership with OAD Technologies provides the technical depth required to outpace evolving threats. The 2026 landscape features AI-driven exfiltration techniques that bypass traditional signature-based tools. We counter these with architectural precision, ensuring your security investments deliver a measurable ROI through reduced downtime and avoided regulatory fines. Our commitment to high-quality craftsmanship means we don’t just solve today’s problems; we anticipate tomorrow’s vulnerabilities.
The Intersection of Human Expertise and Advanced Machine Capability
Our expert architects don’t just monitor logs; they interpret business risk. They translate technical telemetry from SIEM and EDR platforms into actionable intelligence that reflects your unique organizational DNA. We recognize that automated tools often lack the context of business logic. By applying human insight to machine-scale data, we eliminate the “noise” of false positives and focus resources on genuine threats to your digital assets.
Bespoke security engineering is the core of our delivery model. We tailor every aspect of your cloud data loss prevention strategy to fit your specific workflows, whether you’re managing sensitive healthcare records or high-volume financial transactions. This customized approach ensures that security becomes an accelerator for innovation rather than a roadblock. OAD Technologies serves as the dedicated guardian of your long-term digital relevance in an ever-shifting global market.
Build your secure foundation today. Digital transformation requires a partner who understands that your data is your most valuable asset. Contact OAD Technologies to engineer a resilient future for your enterprise.
Architecting Resilience for the 2026 Data Landscape
Legacy security models can’t keep pace with the 75% of enterprise data Gartner predicts will live at the edge by 2026. Transitioning to a modern cloud data loss prevention strategy requires more than off-the-shelf software; it demands a fusion of Zero Trust architecture and AI-driven monitoring. By prioritizing end-to-end GRC integration and rigorous technical assessments, your organization moves beyond reactive patching toward a proactive, future-proof posture. This shift ensures compliance with the UAE Data Protection Law while maintaining the operational speed your business requires.
OAD Technologies serves as your Expert Architect in this journey. We leverage specialized UAE market expertise to navigate complex multi-cloud environments, ensuring your security framework is as ambitious as your growth targets. We don’t believe in one-size-fits-all fixes. Instead, we build high-precision systems that empower your team and protect your most valuable digital assets. It’s time to transform your security from a friction point into a strategic advantage.
Secure your enterprise assets with a bespoke DLP strategy from OAD Technologies.
The path to a more secure digital future in the Emirates starts with a single, well-engineered step. You’ve got the vision; we’ve got the blueprint to make it a reality.
Frequently Asked Questions
What is the first step in creating a cloud data loss prevention strategy?
The first step is executing a comprehensive data discovery and classification audit to identify where sensitive information resides across your cloud environment. You can’t protect what you can’t see. According to Gartner’s 2024 Strategic Roadmap, 60% of organizations fail at DLP because they skip this initial inventory phase. We prioritize mapping data flows to ensure your cloud data loss prevention strategy aligns with specific business risks and operational requirements from day one.
How does cloud DLP differ from traditional on-premise solutions?
Cloud DLP focuses on data in transit and at rest within distributed environments, while traditional solutions rely on a fixed network perimeter. On-premise tools often struggle with the 80% of enterprise traffic that now bypasses the corporate network. Modern cloud-native architectures utilize API integrations and service-side inspection. This shift allows for real-time visibility across SaaS and IaaS platforms, providing the scalability needed for 2026’s decentralized workforce and complex digital ecosystems.
Can cloud DLP help with compliance for the UAE Personal Data Protection Law?
A robust cloud data loss prevention strategy is essential for meeting the requirements of the UAE Personal Data Protection Law, specifically Federal Decree-Law No. 45 of 2021. These tools automate the identification of PII belonging to UAE residents, ensuring data sovereignty and proper consent management. By implementing automated redaction and encryption, firms avoid heavy penalties outlined in the law, which can reach millions of AED for severe non-compliance incidents.
What are the most common challenges when implementing a DLP strategy?
High false positive rates and architectural complexity are the primary hurdles for most enterprises. A 2023 industry survey revealed that 54% of IT teams feel overwhelmed by alert fatigue from poorly tuned policies. Over-restricting data also creates bottlenecks that stall digital transformation. We solve this by designing bespoke policies that distinguish between legitimate business processes and actual threats, ensuring your security framework supports rather than hinders your strategic growth.
Is AI necessary for an effective cloud data loss prevention strategy in 2026?
AI is mandatory for handling the volume and variety of data expected by 2026. Traditional regex-based rules can’t keep up with unstructured data or sophisticated exfiltration techniques. By integrating machine learning, your system gains the ability to understand context and user intent. This reduces manual oversight requirements by 40% while identifying subtle anomalies that indicate a breach. It’s about empowering your team with tools that think as fast as the market moves.
How do I prevent my DLP strategy from causing user friction?
You prevent friction by implementing just-in-time user education and transparent policy enforcement. Instead of hard blocks that stop work, use pop-up notifications that explain why a specific action is risky. This collaborative approach turns employees into active participants in your security posture. Statistics show that interactive training reduces repeat policy violations by 35%. This allows for a seamless integration of security into the daily employee workflow without sacrificing operational efficiency.
What is the role of CASB in a modern cloud DLP framework?
A Cloud Access Security Broker acts as the enforcement point between your users and cloud service providers. It extends your DLP policies to third-party apps like Slack or Salesforce, which are often blind spots in older frameworks. In a 2026 architectural model, the CASB provides the granular visibility needed to monitor shadow IT. It ensures that sensitive data remains encrypted even when shared outside your immediate corporate control, future-proofing your data integrity.
Disclaimer
Content by OAD Technologies is for general informational purposes only and does not constitute professional or cybersecurity advice. No warranties are made regarding accuracy or completeness; reliance is at your own risk. OAD Technologies shall not be liable for any direct or indirect losses arising from use of this content.