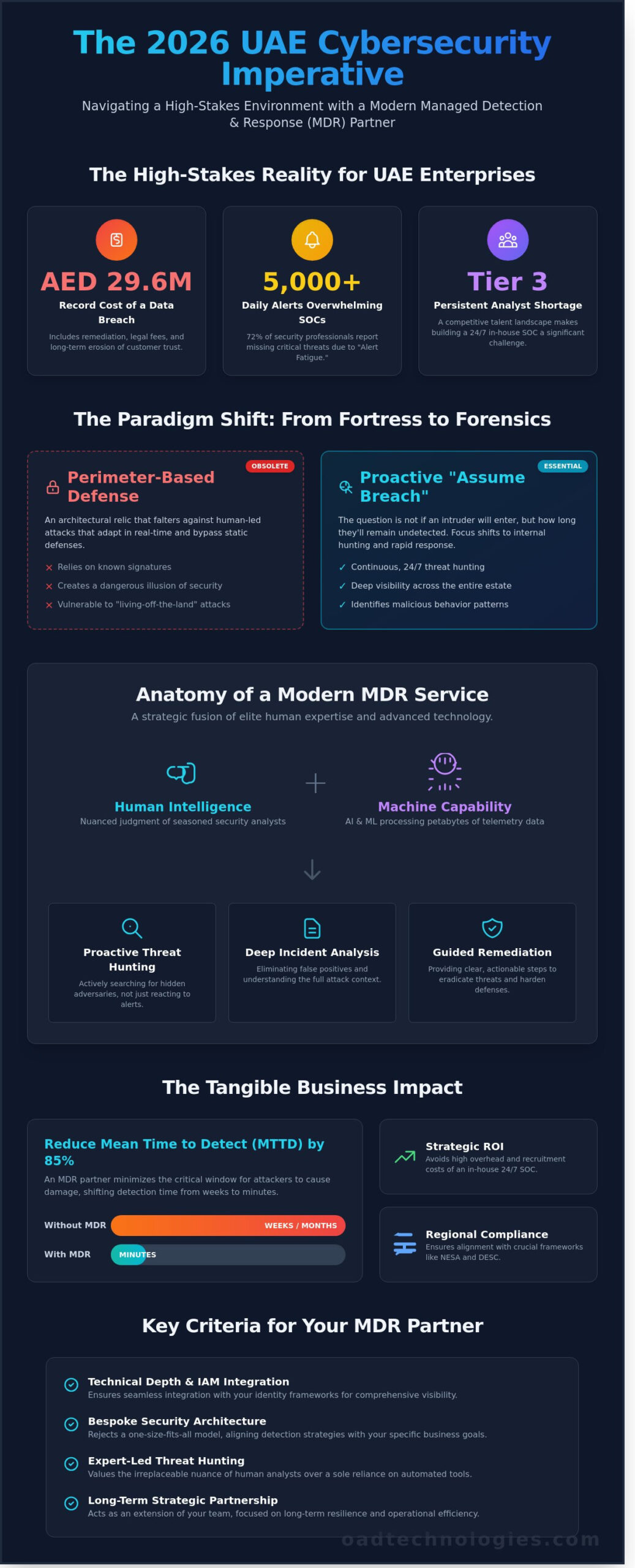
Did you know that the average cost of a data breach for enterprises in the UAE reached a record AED 29.6 million in 2023? You likely recognize the weight of this figure as your SOC team struggles to filter through 5,000 daily alerts while facing a persistent shortage of specialized Tier 3 analysts. It’s clear that simply adding more software isn’t the answer to the sophisticated ransomware targeting our regional infrastructure. Selecting a bespoke mdr service is about more than just outsourcing; it’s about securing a strategic partner who understands the nuances of NESA and DESC compliance.
We’ll help you move beyond the noise of traditional tools to build a resilient, expert-led security posture that scales with your digital transformation. This guide provides the architectural framework to reduce your Mean Time to Detect (MTTD) by 85% and ensure your enterprise remains future-proof against the threats of 2026. You’ll learn how to transition from managing alerts to proactive threat hunting with a partner that values precision and long-term operational efficiency.
Key Takeaways
- Shift from perimeter-based defense to a proactive “assume breach” mentality to counter the sophisticated, human-led cyber threats prevalent in 2026.
- Understand the essential components of a modern mdr service, where advanced technology and human expertise converge to deliver active threat hunting and guided remediation.
- Compare the strategic ROI of managed solutions against the significant recruitment challenges and high overhead costs of building a 24/7 in-house SOC within the UAE’s competitive talent landscape.
- Identify critical evaluation criteria for selecting a provider, focusing on their technical depth and ability to integrate seamlessly with Identity and Access Management (IAM) frameworks.
- Discover how a bespoke security architecture empowers your internal processes and aligns detection strategies with your specific business goals for long-term digital resilience.
The Evolution of Threat Detection: Why Traditional Security is No Longer Enough
By 2026, the traditional concept of a “secure perimeter” has become an architectural relic. Enterprises across the UAE now operate within an “assume breach” environment where the question isn’t if an intruder will enter, but how long they’ll remain undetected. Automated security tools, while necessary, frequently falter against human-led, multi-stage cyberattacks that adapt in real-time. These adversaries don’t just use scripts; they use intuition to bypass static defenses. Relying solely on software creates a dangerous gap that only a sophisticated mdr service can bridge. We’ve seen that technology alone cannot replace the nuanced judgment of a seasoned security analyst.
The financial stakes have never been higher. Recent data indicates that a significant data breach can cost a Dubai-based enterprise upwards of AED 30 million when accounting for remediation, legal fees, and the long-term erosion of customer trust. Beyond the immediate fiscal impact, the damage to brand reputation in a competitive market like the Middle East is often irreparable. OAD Technologies views security not as a series of barriers, but as a continuous strategic operation that aligns technical resilience with tangible business results. It’s about maintaining operational momentum even when under pressure.
The Rise of Sophisticated Cyberthreats
Cybercriminals now utilize generative AI to craft phishing campaigns that are indistinguishable from legitimate corporate communications. These advanced ransomware strains often bypass traditional EDR by operating in memory or using living-off-the-land techniques. Internal IT departments are drowning in “Alert Fatigue,” with 72% of security professionals reporting that they miss critical threats due to the sheer volume of false positives. In 2026, 24/7 monitoring has transitioned from a best practice to a baseline requirement for national enterprise resilience. Without constant vigilance, an organization remains vulnerable during the high-risk hours between 2:00 AM and 6:00 AM GST when internal teams are often offline.
From Prevention to Managed Detection and Response
The strategic shift toward proactive threat hunting marks a turning point in digital defense. A modern Managed detection and response (MDR) framework provides deep visibility across the entire digital estate, encompassing cloud environments, remote endpoints, and IoT devices. This isn’t about blocking every attempt; it’s about identifying malicious behavior before it escalates into a crisis. By integrating human intelligence with machine learning, a bespoke mdr service ensures that your security posture evolves as fast as the threats themselves. You can explore our comprehensive approach in the managed detection and response pillar to understand how we future-proof your digital operations through expert architecture.
What Defines a Modern MDR Service in 2026?
In 2026, an effective mdr service transcends simple alert monitoring. It functions as a high-fidelity bridge between automated detection and decisive action. The UAE Cyber Security Council reported blocking over 71 million cyberattacks in Q1 2024 alone, proving that a passive defense is no longer viable for enterprise resilience. Modern MDR combines advanced telemetry with human-led security expertise to provide three core pillars: proactive threat hunting, deep incident analysis, and guided remediation. Rather than acting as a distant vendor, the provider becomes an extension of your internal team. This relationship is anchored by Expert Architect oversight, ensuring every deployment is bespoke and aligned with your specific operational goals.
The Intersection of Human Intelligence and Machine Capability
Machine learning excels at processing petabytes of data, yet it often lacks the context to distinguish a legitimate administrative script from a lateral movement attempt. According to Gartner’s Market Guide for MDR, the human element remains the critical differentiator in threat validation. A 24/7 Security Operations Center (SOC) staffed by senior analysts provides the nuance required to eliminate noise. MDR is the strategic application of human expertise to machine-generated data for rapid response. This ensures that when an anomaly occurs, the response is measured and precise. It prevents automated lockouts that might otherwise disrupt business continuity in a high-pressure environment.
- Active Threat Hunting: Analysts don’t wait for alerts; they search for hidden indicators of compromise (IoCs) across the network.
- Contextual Analysis: Senior experts evaluate threats based on your specific business logic and risk profile.
- Direct Accountability: Your MDR partner takes ownership of the detection lifecycle, reducing the burden on internal staff.
Bespoke Integration with Your Existing Stack
Security doesn’t exist in a vacuum. A modern mdr service must enhance your previous investments, such as Data Loss Prevention (DLP), rather than replacing them. The synergy between MDR, SIEM, and EDR creates a unified security posture that protects assets from the local endpoint to the cloud. We move beyond one-size-fits-all templates to build tailored protection frameworks that respect your unique data architecture. By integrating these disparate signals into a single pane of glass, we help you achieve a faster mean time to respond (MTTR). If you’re ready to evolve your defense, you can explore our strategic architecture services to see how we align technology with your business objectives.
This tailored approach ensures that your security stack isn’t just a collection of tools, but a synchronized engine. It allows for scalability as your enterprise grows, providing a roadmap for future-proofing your digital assets against an increasingly complex threat landscape.
Comparing the Landscape: MDR vs. MSSP vs. In-House SOC
Enterprise leaders in Dubai and Abu Dhabi face a critical architectural decision: build a fortress from within or partner with specialized elite forces. The choice between an mdr service, a traditional Managed Security Service Provider (MSSP), or an in-house Security Operations Center (SOC) defines your organization’s resilience for the coming years. While the goal is uniform protection, the execution styles vary significantly in their ability to neutralize modern threats.
Traditional MSSPs often function as log aggregators. They monitor your perimeter and send a notification when a threshold is breached, but they rarely step inside to fix the problem. This “alert-only” model creates a dangerous response gap. According to 2024 industry data, the average cost of a data breach in the Middle East has reached AED 30.2 million, making passive monitoring an expensive gamble. You need a partner that doesn’t just identify the smoke but actively neutralizes the fire.
MDR vs. Traditional MSSP Models
The primary differentiator lies in the transition from passive monitoring to proactive hunting. While MSSPs rely on known signatures and basic compliance reporting, MDR providers use behavioral analysis to find “living off the land” attacks that bypass standard filters. This involves active threat mitigation where the provider takes direct action to isolate compromised endpoints or revoke malicious credentials. For a deeper analysis of these operational differences, explore our SOC vs MDR comparison tailored for regional leaders.
- MSSP: Focuses on perimeter health and compliance; response is usually the client’s internal responsibility.
- MDR: Focuses on deep-network threat detection; includes guided recovery and forensic root-cause analysis.
The Business Case for Outsourcing Detection
Building an in-house SOC in the UAE presents steep financial and recruitment hurdles. To maintain a true 24/7 presence, you need a minimum of eight to twelve full-time specialists to cover shifts, leave, and training. With mid-level cybersecurity salaries in the Emirates often exceeding AED 35,000 per month for specialized talent, the annual payroll alone quickly exceeds AED 3 million. This figure doesn’t include the capital expenditure for advanced SIEM and XDR tooling or the high cost of staff turnover in a competitive market.
An mdr service acts as the “Goldilocks” solution, providing expert-level protection without the massive overhead of internal management. It allows your team to maintain strategic control through transparent dashboards and collaborative playbooks while offloading the “noise” of daily monitoring. This model offers immediate scalability as you migrate to the cloud or expand your digital footprint across the region. It ensures your security posture evolves at the speed of innovation, future-proofing your enterprise against the sophisticated attacks expected in 2026.
Strategic Evaluation: How to Choose Your MDR Provider
Selecting an mdr service requires a shift from evaluating software features to auditing operational maturity. Marketing brochures often mask technical gaps; therefore, your evaluation must penetrate the surface of the provider’s security operations center (SOC). You’re not just buying a license. You’re hiring an extension of your engineering team. This partnership succeeds only if the provider demonstrates technical depth that matches your specific architectural needs.
Integration is the primary hurdle for enterprise security. A provider must prove they can ingest and normalize data from your existing stack, specifically your Identity and Access Management (IAM) and cloud-native environments. If their visibility stops at the endpoint, they’ll miss the 80% of breaches that involve compromised credentials. Demand to see documented incident response workflows that show exactly how they transition from detection to active remediation. You need a partner who doesn’t just send alerts but executes pre-approved containment actions.
Reporting needs to serve two masters. Technical leads require granular forensic data and raw telemetry to understand the “how” of an attack. Conversely, C-suite executives need metrics that translate risk into business impact. In the Middle East, where the average cost of a data breach reached AED 29.6 million in 2023 according to IBM reports, your reporting should clearly demonstrate ROI through risk reduction and operational uptime.
Key Technical Questions for Potential Partners
Bespoke playbooks are non-negotiable. Off-the-shelf responses fail because they don’t account for your industry’s unique risk profile. Ask potential partners if they customize detection logic based on your specific crown jewels. You should also verify their Mean Time to Respond (MTTR). In a 2026 threat environment, a critical incident response must initiate within minutes, not hours. For a structured comparison of these metrics, utilize the MDR provider selection checklist to ensure no technical requirement is overlooked.
Compliance and GRC Alignment
Data residency is a critical pillar for UAE enterprises. Your provider must align with the UAE Data Protection Law (Federal Decree-Law No. 45 of 2021) and specific sector regulations like NESA or DESC. An effective mdr service acts as a continuous audit mechanism, providing the evidentiary logs required for Governance, Risk, and Compliance (GRC) frameworks. They shouldn’t just secure your perimeter; they should simplify your regulatory reporting by mapping detections to specific compliance controls.
Ready to build a resilient security architecture? Consult with OAD Technologies to design a bespoke MDR strategy tailored to your enterprise needs.
The OAD Technologies Approach: Bespoke MDR for Enterprise Resilience
OAD Technologies views security as a foundational architecture rather than a peripheral tool. We believe an effective mdr service should empower your existing team and refine your internal processes. We don’t believe in rigid templates. Instead, we craft detection strategies that mirror your specific operational risks within the UAE’s unique regulatory environment. Our philosophy centers on the intersection of human intelligence and machine capability, ensuring that technology serves the people who manage it.
We develop tailored detection strategies that align with your commercial goals. If your priority is protecting critical infrastructure in Abu Dhabi or securing financial data in Dubai, our logic adapts to those specific threats. We go beyond simple monitoring by providing a clear roadmap for your long-term digital relevance. This means we help you anticipate shifts in the market and technology, ensuring your security posture supports future scalability rather than hindering it.
Successful integration is the hallmark of our engineering standards. We create a unified visibility layer across your network and email systems. We also provide seamless connectivity with your cloud security (CSPM). This holistic view allows us to track threats as they move laterally across different environments, closing the gaps that traditional, siloed security tools often miss.
Expert Architects at Your Service
Our senior engineers act as a direct extension of your internal department. You won’t deal with entry-level analysts; you get immediate access to strategic consultants who solve complex digital hurdles. We maintain a can-do attitude that’s grounded in rigorous engineering. This collaborative spirit ensures we don’t just identify problems. We solve them alongside your team, adhering to NESA and DESC standards to ensure local compliance remains airtight.
Future-Proofing Your Digital Assets
Security logic must evolve faster than the 2026 threat landscape. We continuously update our detection protocols to counter sophisticated AI-driven exploits and zero-day vulnerabilities. This strategic partnership focuses on long-term growth and operational resilience, protecting your ROI as you expand your digital footprint. Our mdr service provides the stability you need to innovate with confidence. OAD Technologies remains dedicated to bridging high-level technical innovation with grounded, measurable business results for the modern enterprise.
Future-Proofing Your Enterprise Defense
By 2026, enterprise security isn’t just about blocking known threats; it’s about anticipating the unknown. You’ve seen that traditional MSSPs often fail to provide the deep architectural integration required for modern DLP and IAM stacks. Choosing a sophisticated mdr service is now a strategic requirement for any UAE organization aiming to align with national GRC frameworks and maintain operational resilience. OAD Technologies delivers this through an expert-led SOC that conducts 24/7 proactive threat hunting. We don’t believe in generic templates. Our team builds bespoke security architectures that integrate directly into your existing infrastructure. This ensures your business meets the rigorous standards set by UAE regulatory bodies while optimizing your digital performance.
Secure your enterprise future with a bespoke MDR strategy from OAD Technologies
Your journey toward a more resilient digital presence starts with a partner who understands the local landscape and the global threat horizon. We’re ready to help you build a defense that grows with your ambition.
Frequently Asked Questions
What is the primary difference between a managed security service provider (MSSP) and an MDR service?
An MSSP primarily focuses on log management and perimeter monitoring, whereas an mdr service prioritizes active threat hunting and rapid incident response. While an MSSP might alert you to a potential issue, an MDR provider uses advanced telemetry to neutralize threats within your network. This proactive approach reduces the mean time to detect (MTTD) from the 2023 industry average of 204 days down to mere minutes.
Can an MDR service replace my existing internal security team?
An MDR service doesn’t replace your internal staff; it empowers them by handling the 24/7 burden of alert triage and threat analysis. This partnership allows your UAE-based team to focus on high-level digital transformation and strategic growth initiatives. By offloading 95% of routine security noise, your engineers can reclaim 40 hours per week for architectural improvements and bespoke business projects.
How does an MDR service help with national regulatory compliance and GRC?
MDR services align your security operations with UAE-specific mandates such as the NESA (National Electronic Security Authority) standards and DESC (Dubai Electronic Security Center) requirements. These services generate the auditable logs and incident reports necessary for ISO 27001 certification and the UAE Data Protection Law. Using a tailored mdr service ensures your organization meets the strict 2024 reporting timelines for data breaches.
What happens during the first 24 hours of an MDR service identifying a critical threat?
Within the first 60 minutes, the MDR team isolates infected endpoints to stop lateral movement across your network. By the four-hour mark, analysts complete a forensic investigation and initiate a bespoke remediation plan to neutralize the attacker. Within 24 hours, you’ll receive a comprehensive root-cause analysis and a strategic roadmap to prevent similar vulnerabilities from being exploited again.
Is an MDR service effective for multi-cloud and hybrid environments?
Yes, an MDR service provides seamless integration across AWS, Azure, and on-premises data centers located in the UAE. It aggregates security telemetry into a single pane of glass, eliminating the blind spots that often lead to breaches. This visibility is essential because 82% of data breaches in 2024 involved cloud-based assets, requiring a unified defense strategy that spans all environments.
How does MDR integrate with my existing Data Loss Prevention (DLP) strategy?
MDR enhances your DLP strategy by providing the behavioral context needed to distinguish between normal business processes and malicious data exfiltration. When a DLP tool flags a sensitive file transfer, the MDR service analyzes the user’s intent and the health of the endpoint. This integrated approach reduces false positive rates by 60%, ensuring your business stays operational without compromising data integrity.
What metrics should I use to measure the ROI of an MDR service?
You should measure ROI by tracking the reduction in Mean Time to Respond (MTTR) and the total cost of ownership compared to a 24/7 in-house SOC. A successful deployment often prevents a breach, which costs UAE firms an average of AED 25 million according to 2023 industry reports. Focus on operational efficiency gains and the potential reduction in cyber insurance premiums as key financial indicators.
Does an MDR service provide remediation or just detection alerts?
Modern MDR services provide active remediation, which means they take direct action to neutralize threats rather than just sending alerts. This includes killing malicious processes, rolling back encrypted files, and updating firewall rules in real time. By moving beyond simple detection, these services achieve a 90% faster response rate than traditional models, significantly limiting the impact of any security incident.
Disclaimer
Content by OAD Technologies is for general informational purposes only and does not constitute professional or cybersecurity advice. No warranties are made regarding accuracy or completeness; reliance is at your own risk. OAD Technologies shall not be liable for any direct or indirect losses arising from use of this content.