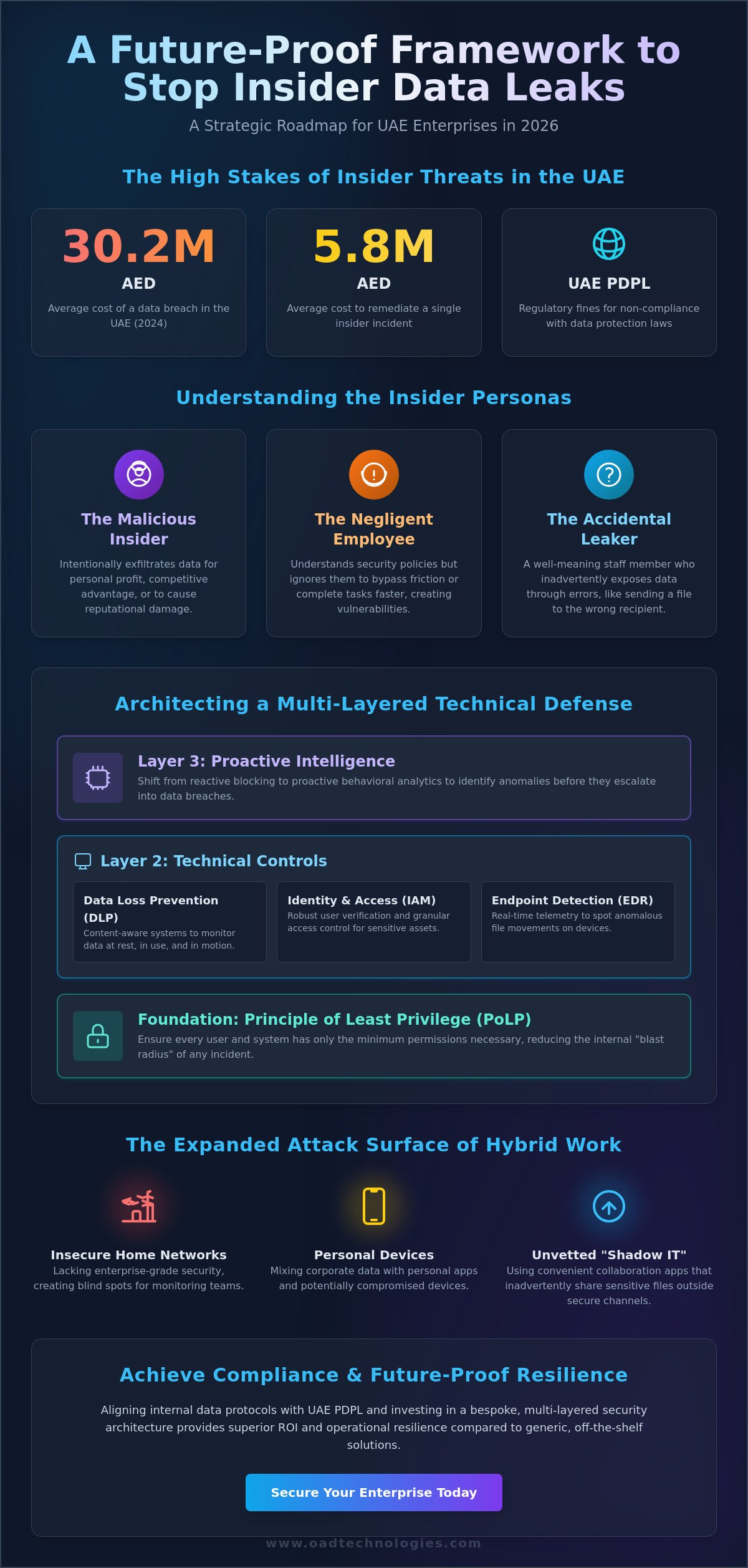
The 2023 Cost of Insider Threats Global Report reveals that the average annual cost to remediate a single insider incident in the Middle East now exceeds 5.8 million AED. You’ve likely felt the tension of trying to empower your workforce while fearing that a single accidental upload or intentional export could trigger massive regulatory fines under the UAE PDPL. It’s a complex challenge to distinguish between standard operational workflows and the early stages of data exfiltration, especially when your intellectual property is your most valuable currency.
This guide provides a definitive roadmap on how to stop employees from leaking data by implementing a sophisticated, multi-layered framework designed for the 2026 digital environment. We’ll explore how to integrate advanced behavioral monitoring with bespoke governance strategies to secure your enterprise perimeter without compromising your team’s operational momentum. By the end of this article, you’ll have a future-proof strategy to maintain compliance with national data protection standards while fostering a culture of accountability and precision.
Key Takeaways
- Identify the critical differences between malicious, negligent, and accidental insiders to tailor your enterprise security response to specific behavioral risks.
- Learn how to stop employees from leaking data by architecting a multi-layered defense that integrates advanced Data Loss Prevention (DLP) with robust Identity and Access Management (IAM).
- Shift from reactive, signature-based detection to proactive behavioral analytics to identify and mitigate anomalies before they escalate into data breaches.
- Align your internal data handling protocols with the UAE Personal Data Protection Law (PDPL) to ensure regulatory compliance and strengthen institutional governance.
- Discover why bespoke, future-proofed security architectures provide superior ROI and operational resilience compared to generic, off-the-shelf software solutions.
The Insider Threat Landscape: Why Employees Leak Data
Employee data leakage occurs when sensitive corporate information moves from secure internal environments to unauthorized external destinations. While external cyberattacks often capture headlines, the internal vector remains the most complex challenge for UAE enterprises. To understand how to stop employees from leaking data, leadership must first analyze the Insider Threat Landscape and the personas that drive these incidents.
- The Malicious Insider: An individual who intentionally exfiltrates data for personal profit, competitive advantage, or to damage the firm’s reputation.
- The Negligent Employee: A worker who understands security policies but chooses to ignore them to complete tasks faster or bypass bureaucratic friction.
- The Accidental Leaker: A well meaning staff member who inadvertently exposes data through clerical errors, such as sending a sensitive spreadsheet to the wrong recipient.
The financial stakes for organizations in Dubai and Abu Dhabi are immense. In the Middle East, specifically within the UAE and Saudi Arabia, the average cost of a data breach reached approximately AED 29.6 million in 2023. Beyond immediate financial loss, organizations face severe regulatory penalties under the UAE Data Protection Law (Federal Decree Law No. 45 of 2021) and lasting reputational damage that erodes client trust. Traditional perimeter defenses like firewalls fail in this context because they’re designed to keep intruders out, not to monitor those who already hold authorized access to the kingdom’s most valuable assets.
Intentional vs. Unintentional Exfiltration
Intentional theft often stems from a desire for direct financial payout on the dark web or securing a competitive edge for a future employer. Conversely, unintentional leaks happen through sophisticated phishing campaigns, misconfigured cloud storage, or the use of unvetted “shadow IT” tools. Insider Risk is the potential for an individual with authorized access to negatively impact the organization. Identifying these risks requires a shift from reactive blocking to proactive behavioral analysis that respects the balance between security and productivity.
The Evolving Risks of Remote and Hybrid Work
The transition to hybrid work models has expanded the attack surface significantly. Home networks and personal devices often lack the enterprise grade security layers found in corporate offices, creating blind spots for security teams. Employees frequently use collaboration apps for convenience, inadvertently sharing sensitive files outside secure channels. Achieving total visibility into these data movements is the first critical step in learning how to stop employees from leaking data while ensuring the organization’s future-proofing against emerging digital threats.
Architecting a Multi-Layered Technical Defense
Building a resilient perimeter requires moving beyond simple firewalls toward a sophisticated, multi-layered architecture. At the core of this strategy lies the Principle of Least Privilege (PoLP). This foundational rule ensures that every user, process, or system has only the minimum permissions necessary to perform its function. By restricting access by default, you significantly reduce the internal “blast radius” should a credential be compromised or a staff member act maliciously. Technical defense isn’t a single wall; it’s a dynamic ecosystem designed to monitor and control every data interaction.
Visibility is the second pillar of this architecture. Endpoint Detection and Response (EDR) provides the telemetry needed to spot anomalous file movements or unauthorized software execution in real-time. Without this granular oversight, identifying how to stop employees from leaking data becomes a reactive game of catch-up rather than a proactive defense. In the UAE, where the average cost of a data breach reached AED 30.2 million in 2024 according to IBM, these technical controls are no longer optional; they’re business imperatives that protect the bottom line.
Deploying Enterprise-Grade DLP Solutions
Modern Data Loss Prevention (DLP) strategies have evolved into content-aware systems that analyze the context of data, not just its file type. These solutions identify sensitive information whether it’s at rest in a database, in use within an application, or in motion across a network. Instead of blanket blocks that hinder productivity, bespoke DLP configurations use machine learning to distinguish between a legitimate business transfer and a potential leak. This level of intelligence is central to understanding how to stop employees from leaking data without disrupting the daily workflow or frustrating your high-performing teams.
Strengthening Access with IAM and Zero Trust
Identity is the new perimeter. Implementing robust Identity and Access Management (IAM) frameworks is essential for verifying every request. While Multi-Factor Authentication (MFA) is the bare minimum, a Zero Trust approach assumes no user is inherently trustworthy, even within the corporate network. This requires understanding insider threat types ranging from the accidental sharer to the malicious actor who intentionally bypasses security protocols.
To further harden the environment, enterprises should adopt Just-in-Time (JIT) access. This grants elevated privileges only for the specific duration needed to complete a task, effectively closing the window of opportunity for data exfiltration. If you’re looking to future-proof your infrastructure, OAD Technologies can help you design a tailored security roadmap that aligns with your specific risk profile and UAE regulatory requirements like NESA and the UAE Data Protection Law.
Monitoring Behavior and Detecting Anomalies
Traditional security perimeters often fail because they focus on keeping outsiders away while ignoring the activity within the network. To understand how to stop employees from leaking data, enterprises must transition from static, signature-based detection to dynamic behavioral analytics. Security Information and Event Management (SIEM) and Managed Detection and Response (MDR) act as the central nervous system of this strategy; they provide the visibility required to distinguish between a productive employee and a potential insider threat.
Modern defense relies on User and Entity Behavior Analytics (UEBA). This technology establishes a baseline of “normal” for every user. When an account suddenly deviates from its standard patterns, the system triggers an alert. We believe the most effective security architectures combine this machine precision with human intelligence. Automated systems catch the speed of the attack, but expert analysts provide the context needed to validate whether an alert is a genuine threat or a simple procedural error by a well-meaning staff member.
Identifying High-Risk Behavioral Signals
Detecting an insider threat early requires monitoring for specific digital breadcrumbs. In the UAE market, where digital transformation is accelerating, organizations often face risks from “Flight Risk” profiles. These are employees who, during their notice period or following a performance review, begin implementing layered security controls to bypass standard protocols. Key signals include:
- Massive data downloads or exports at unusual hours, such as 3:00 AM GST.
- Accessing sensitive directories or “crown jewel” assets that the employee never utilized in the previous 12 months.
- Unauthorized use of personal cloud storage or encrypted USB drives, which often signal intent to exfiltrate IP before a departure.
Managed Detection and Response (MDR) for Rapid Containment
Detection is only half the battle; speed of response determines the total cost of a breach. Our Managed Detection and Response (MDR) services provide 24/7 oversight, ensuring that suspicious data movement is investigated in real-time. This is critical because a 2024 study indicated that the average cost of an insider-related incident can exceed 55 million AED for large enterprises if not contained within 30 days.
Effective MDR utilizes automated playbooks to halt exfiltration instantly. If the system detects a high-risk data transfer to an unapproved external domain, it can automatically isolate the endpoint or revoke the user’s credentials. This proactive stance ensures that the data stays within the organization while security teams conduct a forensic review. It’s a bespoke approach to resilience that prioritizes business continuity without sacrificing data integrity. By bridging the gap between high-level innovation and practical results, these systems empower your team to act before the damage is done.
Establishing a National Standard of Data Governance
The UAE digital economy is projected to contribute AED 514 billion to the national GDP by 2031, making data the most valuable currency in the region. For enterprise leaders determining how to stop employees from leaking data, the strategy must align with the UAE Personal Data Protection Law (PDPL). This legal framework isn’t a mere checklist; it’s a blueprint for operational integrity. By synchronizing leak prevention with PDPL mandates, firms ensure that sensitive information stays within sovereign borders while maintaining international trust.
Security culture requires more than an annual seminar. Research indicates that 82% of data breaches involve a human element, whether through social engineering or simple negligence. We move beyond static training by implementing continuous, behavior-based learning modules that adapt to current threat vectors. This approach transforms employees from potential liabilities into active participants in the firm’s defense perimeter.
Compliance as a Strategic Advantage
Technical controls do more than block unauthorized transfers; they satisfy specific regulatory requirements for data sovereignty and residency. Implementing a Governance Risk and Compliance (GRC) strategy allows your organization to view security through a lens of risk management rather than just IT maintenance. GRC frameworks bridge the gap between policy and technical execution by ensuring every automated security protocol maps directly to a legal obligation. This alignment protects the board from liability while streamlining the audit process for local regulators.
Step-by-Step Data Leak Prevention Policy Implementation
- Step 1: Conduct a data discovery and classification exercise. You can’t protect what you can’t see. Use automated tools to scan your environment and label data based on sensitivity levels defined by UAE standards.
- Step 2: Define clear “Acceptable Use” policies for all employees. Eliminate ambiguity by documenting exactly how corporate data should be handled on mobile devices, cloud apps, and remote connections.
- Step 3: Implement tiered access based on job roles and data sensitivity. Apply the principle of least privilege. Grant access only to the specific datasets required for an employee’s daily functions; nothing more.
- Step 4: Establish a clear incident response plan for suspected leaks. Define the chain of command and notification protocols to meet the PDPL’s reporting timelines if a breach is detected.
Effective governance also demands a rigorous offboarding protocol. Ghost access, where former employees retain active credentials, is a critical vulnerability in the UAE’s high-mobility job market. Your system must automate the revocation of all digital identities within minutes of a contract termination. This immediate severance of access is a fundamental step in how to stop employees from leaking data during sensitive transition periods. We help organizations build these resilient frameworks to ensure long-term digital relevance.
Ready to secure your enterprise against internal threats? Consult with our expert architects to design a bespoke data governance framework today.
Future-Proofing Your Enterprise with OAD Technologies
Generic, off-the-shelf security software often fails because it treats every enterprise like a carbon copy. These tools provide a rigid blanket of protection that creates blind spots in complex, high-growth environments. When your organization is evaluating how to stop employees from leaking data, a one-size-fits-all approach isn’t just ineffective; it’s a financial risk. OAD Technologies functions as an Expert Architect, designing bespoke security frameworks that align with your specific business logic and operational goals. We don’t just sell software. We build resilient ecosystems that bridge the gap between visionary innovation and practical, measurable results.
Our methodology focuses on becoming a seamless extension of your internal team. We understand that security must support, not stifle, your digital transformation. By integrating our engineering standards directly into your workflow, we ensure that every security layer adds value to your ROI. This collaborative partnership allows us to solve complex challenges with precision, moving beyond simple patches to create long-term stability. We prioritize high-quality craftsmanship to ensure your data remains your most secure asset as you scale.
- Strategic Alignment: We map security protocols to your specific business processes.
- Operational Efficiency: Our solutions reduce the friction often caused by intrusive security measures.
- Technical Authority: We leverage the latest exfiltration prevention techniques tailored for 2026.
- Direct Accountability: We take ownership of the technical architecture, providing a clear roadmap for success.
Bespoke Security Architecture for the UAE Market
The UAE digital landscape is unique, shaped by rapid innovation and strict regulatory requirements such as NESA and the UAE Data Protection Law. A security stack designed for a different market won’t offer the localized resilience you need. We design architectures that grow with your digital transformation, ensuring you’re prepared for evolving threats. A cornerstone of this strategy involves continuous technical assessments. Our VAPT services provide a rigorous audit of your defenses, simulating real-world exfiltration attempts to find vulnerabilities before they’re exploited. In 2025, reports indicated that 42% of Middle Eastern data breaches involved compromised internal credentials. Our bespoke approach addresses these specific regional risks with precision.
Get Started with a Data Security Assessment
Understanding how to stop employees from leaking data begins with absolute visibility. If you can’t see how data moves across your hybrid network, you can’t protect it. We invite you to audit your current visibility through a comprehensive Data Security Assessment. OAD Technologies applies rigorous engineering standards to identify where your data is most at risk. We don’t believe in quick fixes; we believe in building a foundation for long-term digital relevance. Contact an Expert Architect today to schedule your consultation and secure your enterprise’s future in the UAE market.
Securing Your Enterprise Legacy in the 2026 Landscape
Modern data protection requires more than just firewalls; it demands a fusion of human intelligence and machine capability. You’ve seen that the path to resilience involves architecting a multi-layered defense and strictly adhering to the UAE Personal Data Protection Law (PDPL). By 2026, the complexity of insider threats will only intensify. Understanding how to stop employees from leaking data isn’t just a technical requirement; it’s a strategic imperative for long-term operational growth. OAD Technologies acts as your Expert Architect, bridging the gap between high-level GRC requirements and practical business results. We don’t believe in one-size-fits-all software. Instead, we provide bespoke strategies that leverage seamless integration between Managed Detection and Response (MDR) and Data Loss Prevention (DLP) technologies. This ensures your UAE-based enterprise meets global standards while maintaining local compliance. Your digital transformation deserves a foundation built on precision and visionary engineering. Secure your assets with a bespoke DLP strategy from OAD Technologies. The future of your data is secure when technology and strategy work in perfect harmony.
Frequently Asked Questions
How can I tell if an employee is planning to steal data?
Look for behavioral anomalies and unusual technical activity across your network. Research from 2024 indicates that 85% of insider threats exhibit identifiable indicators before an incident occurs. Watch for access requests to sensitive files outside typical working hours or sudden spikes in data egress. OAD Technologies implements User and Entity Behavior Analytics (UEBA) to flag these deviations automatically, providing the foresight needed to intervene before a breach happens.
Is monitoring employee activity legal under UAE data protection laws?
Yes, monitoring is legal provided it complies with the UAE Federal Decree-Law No. 45 of 2021 on Personal Data Protection. Companies must establish a clear legal basis and notify employees through a transparent data privacy policy. In the UAE, the Data Office oversees these regulations. You must ensure the monitoring is proportionate to the risk and focused on protecting business assets rather than infringing on the private lives of your staff.
What is the most common way employees leak data accidentally?
Misdirected emails and unauthorized cloud storage use remain the primary drivers of accidental leaks. A 2023 industry report indicates that 43% of data breaches result from human error, often involving sending sensitive documents to the wrong recipient. Employees frequently use personal cloud accounts to finish work at home, bypassing enterprise security. This is a critical factor when considering how to stop employees from leaking data effectively through unintentional actions.
Can DLP software block employees from using personal USB drives?
Yes, modern Data Loss Prevention (DLP) solutions can enforce strict device control policies. You can configure these systems to block all unauthorized USB devices or restrict them to read-only mode. In 2025, enterprise-grade DLP tools integrate with endpoint security to verify the hardware ID of every peripheral. This ensures only company-issued, encrypted drives can interact with your sensitive data architecture, preventing unauthorized physical transfers of intellectual property or client records.
How does Zero Trust help in stopping data leaks?
Zero Trust operates on the principle of never trust, always verify, eliminating implicit trust within the network. By segmenting the network and requiring continuous authentication, you limit the blast radius of any potential leak. Even if an employee has valid credentials, they only access the specific resources required for their role. This architecture reduces unauthorized data movement by up to 50% in complex enterprise environments by treating every access request as a potential risk.
What should I do immediately if I suspect a data leak has occurred?
Activate your Incident Response Plan and isolate the affected systems instantly. Your first 60 minutes are critical for containment. Identify the source of the leak, revoke the user’s access credentials, and preserve all digital logs for forensic analysis. Under UAE Law No. 45, you may also have legal obligations to report the breach to the UAE Data Office within 72 hours if personal data is compromised, so legal consultation is vital.
How often should we update our data protection policies?
Review and update your data protection policies at least every 12 months or after any significant infrastructure change. The threat landscape evolves rapidly, with 70% of UAE enterprises reporting more sophisticated social engineering attacks in 2024. Regular updates ensure your protocols address new technologies like generative AI and evolving regulatory requirements. This proactive approach is a cornerstone of how to stop employees from leaking data in a shifting digital economy.
Disclaimer
Content by OAD Technologies is for general informational purposes only and does not constitute professional or cybersecurity advice. No warranties are made regarding accuracy or completeness; reliance is at your own risk. OAD Technologies shall not be liable for any direct or indirect losses arising from use of this content.